Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Maximizing and Optimizing Your Splunk Enterprise Security
Uncovering thousands of unique secrets in PyPI packages
Security Researcher Tom Forbes worked with the GitGuardian team to analyze all the code committed to PyPi packages and surfaced thousands of hardcoded credentials.
Your WordPress Data Exposure Risks
Unlocking the Power of Co-Managed SOC: A Strategic Solution for Maximizing SIEM Effectiveness and Cybersecurity Success
Security information and event management (SIEM) systems play a pivotal role in cybersecurity: they offer a unified solution for gathering and assessing alerts from a plethora of security tools, network structures, and software applications. Yet, the mere presence of a SIEM isn't a magic bullet. For optimal functionality, SIEM systems must be appropriately set up, governed, and supervised round-the-clock.
Securely disposing of old electronics and data: A forensic guide to protecting your information
In our rapidly evolving digital landscape, the accumulation of old electronic devices is a common occurrence. Laptops, smartphones, external hard drives, and USB flash drives quickly become outdated and obsolete, yet they often contain a wealth of sensitive information. Safeguarding your personal and confidential data during the disposal process is of utmost importance.
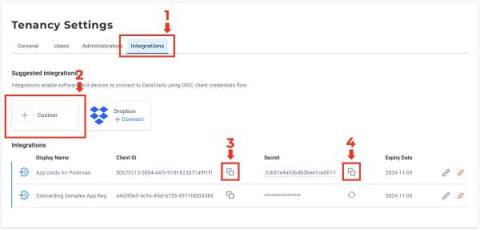
Postman Configuration for DataTrails
One of my favourite tools for playing with REST APIs is, of course, Postman. It can make interacting with DataTrails super quick and easy, and help you develop custom workflows for storing and validating your digital provenance and audit trails. Here’s a step-by-step guide to getting a robust Postman set-up configured, and if you head over the Postman public collections you’ll find a link to a pre-baked DataTrails Postman collection with this done for you, along with some example requests.
Cyber Attack Preparedness
Rubrik has been assisting our customers with recovery from cyber attacks since 2018. We immediately took notice of these attacks, and early on, began developing processes and procedures to respond more effectively to better assist our customers. Our spirit of continuous improvement and execution of lessons learned from the field has led to a number of improvements to both our products and processes.