Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Testimonial Video about Ignyte
So You Want to Achieve NERC CIP-013-1 Compliance...
Is an electricity provider’s supply chain its weakest link in the event of a cyberattack? The evidence is compelling that third parties often play unwitting roles. For example, the NotPetya ransomware attacks in mid-2017 originally gained a foothold via a backdoor in third-party accounting software. To safeguard North America’s electricity supply, the North American Electric Reliability Corporation (NERC) has issued several critical infrastructure protection (CIP) standards.
Ignyte UFCU testimonial video
Ignyte Assurance Platform - Genetisis' testimonial
Google Cloud Platform compliance & Risk Management
Previously we published an article discussing some of the best practices surrounding cloud security, in this article, we will discuss cloud a little more specifically by focusing on one in particular provider Google. Google offers several different solutions for customers known as GCP or the Google Cloud Platform. GCP is set infrastructure tools and services which customers can utilize to build environments they need in order to facilitate a solution for their business.
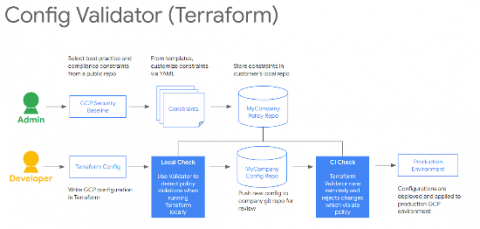
Protecting your GCP infrastructure with Forseti Config Validator part four: Using Terraform Validator
In the previous posts of this series, we discussed how you can secure your infrastructure at scale by applying security policies as code to continuously monitor your environment with the Config Validator policy library and Forseti. In this article, we’ll discuss how you can reuse the exact same policies and Terraform Validator to preventively check your infrastructure deployments, and block bad resources from being deployed in Google Cloud Platform (GCP).
3 Trends Where Technology Can Simplify Vendor Risk Management
Vendor risk management is the practice of governing third-party access to company data. This is a critical aspect of an organization since vendors view your business information when providing their services. For some, this can turn into a severe vulnerability that can lead to data breaches. In fact, in the past five years, vendors like Home Depot and Target were responsible for those incidents, as reported by Forbes.