Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Solarwinds and Cisco 10.0: Big Problems for Big Companies
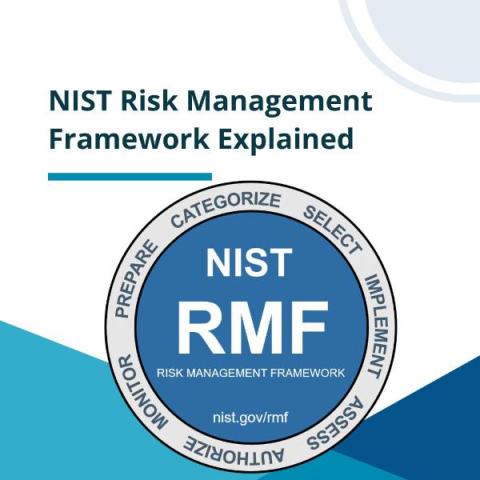
NIST Risk Management Framework (RMF) Explained
Unlock the Power of Quality Data in AI: Data Cleaning for Enhanced Accuracy and Output
Critical Confluence Vulnerability - CVE-2023-22518
CMMC 2.0 Preparation: Top Four Strategic Actions to Take Now
The Cybersecurity Maturity Model Certification (CMMC) 2.0 is a compliance requirement that all Department of Defense (DoD) Contractors (aka, the Defense Industrial Base) will soon have to meet. See my blog Why is CMMC a Big Deal? for more information about the legal implications of CMMC. The CMMC official mandate is expected to be released from rulemaking in the first quarter of 2024 and be in full implementation in the first quarter of 2026.
How Security Ratings Empower CISOs in an Era of Burnout
When I bring up the topic of security ratings to my CISO colleagues, I typically get one of two reactions. The first half complains about misattribution of issues along with reporting fix times (although accuracy has improved). But the other half understand how to leverage this technology to their benefit to make their jobs easier and their organizations safer. Read below to get under the hood of how to leverage the evolving application of this technology to secure your supply chain.
Pirates of the Inbox: Navigating the Dangerous World of Business Email Compromise
Business Email Compromise (BEC) is one of the fastest-growing and financially-damaging cybercrimes. It has consistently led the way in cybercrime losses in recent years. According to the 2022 FBI Internet Crime Report, the FBI received 21,832 Business Email Compromise (BEC) complaints, with estimated losses totalling more than $2.7B. Data shows a 38% increase in cybercrime as a service targeting business email between 2019 and 2022.