Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Act Now to Prepare for New NCUA Cyber Incident Reporting Requirements
We recently discussed the new SEC rule requiring all registered companies to report material cyber incidents within four (4) days.
CISO Global Names Industry Veteran Gary Perkins as Chief Information Security Officer
GDPR and Biometric Data: Ethical Considerations and Privacy Implications
As technology advances and the use of biometric data becomes more prevalent, it is crucial to address the privacy concerns and regulatory compliance associated with this sensitive data. The General Data Protection Regulation (GDPR) plays a key role in safeguarding individuals’ privacy rights and ensuring the responsible handling of biometric data. Artificial Intelligence (AI) can also be utilized to ensure compliance and responsible handling of biometric data.
Vulnerability management: traditional approaches vs. risk-based strategies
As the threat landscape evolves, so must the methods and tools to safeguard critical digital assets. Vulnerability management programs that were once considered the gold standard are starting to show limitations in their ability to address complex cyber risks.
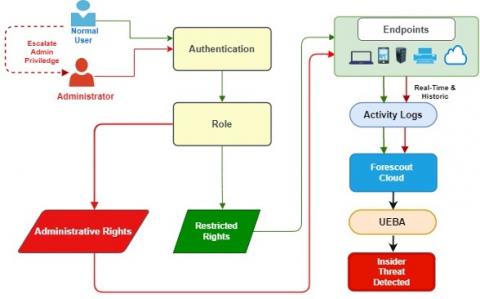
The Hidden Danger - Understanding and Defending Against Insider Threats
Q2 2023 Threat Landscape Report: All Roads Lead to Supply Chain Infiltrations
Kroll’s findings for Q2 2023 reveal a notable shift toward increased supply chain risk, driven not only by the CLOP ransomware gang’s exploitation of the MOVEit transfer vulnerability, but by a rise in email compromise attacks. This and other key security trends are shaping a threat landscape in which diverse cyber threats are present.
Unveiling Infra as Code Security in the GitGuardian Platform
Discover how GitGuardian's new Infra as Code Security capabilities empower cloud engineers and security professionals to detect, manage, and resolve IaC vulnerabilities precisely.
Creating a Physical Security Standard for Your Company
Cybersecurity is the pressing concern most organizations face when it comes to securing data, but not every hacker launches an attack from thousands of miles away; sometimes, the threat can walk right in through the front door to gain access to your IT system. Adversaries are not shy about using a more direct approach, which is why an organization should not overlook its physical security plan.
EP 34 - How to Catch a Malicious Insider w/ Eric O'Neill
Today’s episode of Trust Issues focuses on spycatching! Eric O’Neill, a former FBI counterintelligence operative and current national security strategist, joins host David Puner to discuss his legendary undercover mission to capture Robert Hanssen, one of the most notorious and damaging spies in U.S. history.