Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Mr and Mrs CISO: Security in the Age of the Lockdown
With so many of us frantically learning to juggle our roles as parents, workers and most recently teachers; is it just my wife and I who feel it necessary to monitor the online activity of our teenagers during this lockdown? Sure, there’s rich educational content out there, but it sits amongst social networks, streaming services, gaming consoles and a world of other distractions. I almost miss the days when staring out of the window was a reasonable ‘get out’!
COVID-19 Scam Roundup - March 30, 2020
Many in the digital security community are coming together to combat malicious actors during the coronavirus disease 2019 (COVID-19) global outbreak. One of the most visible of these new efforts is the COVID-19 CTI League. Made up of approximately 400 volunteers living in approximately 40 countries, the COVID-19 CTI League is working to block attackers from health care organizations and other medical facilities at this juncture.
Are You Ready for the Remote Work's Toll on Corporate Security?
Given the situation that many companies, organizations and government agencies have been forced into working remotely due to COVID-19, it is imperative to give some thought about corporate security.
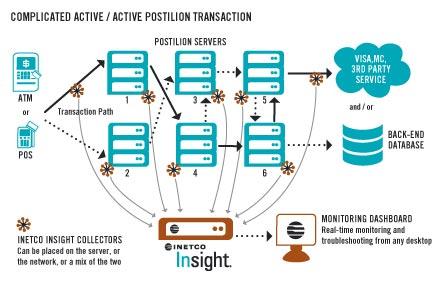
INETCO Insight Active/Active-ly Monitoring Complex Card Network Environments
For many banks, payment processors and card network providers, the main purpose of an active/active architecture is to achieve load balancing, improve throughput and guarantee response times.
Coronavirus Pandemic: Beware of the Bait Sites
The menace of coronavirus pandemic is accelerating significantly and hackers are capitalizing the element of fear to collect shear currency. They are creating thousands of websites as baits. According to the Check Point Research report, threat actors are registering phony COVID-19-related domains and selling them on discounted off-the-shelf malware on the dark web. In this article, we will delve into some essential details regarding the coronavirus-related bait sites. Here is some help.
Top 5 Cybersecurity Threats to Watch in 2020
These days, cybercriminals are ambitious and innovative, with no shortage of tools and resources at their disposal to go after high-stakes targets and execute malicious code — all while flying completely under the radar. To prepare you for what’s ahead, below are five of the top cybersecurity threats you might encounter in 2020.
Now Is the Time to Get up to Speed with CMMC and SP 800-171 Rev 2
At the beginning of March 2020, Fifth Domain reported that Colorado-based aerospace, automotive and industrial parts manufacturer Visser Precision LLC had suffered a DoppelPaymer ransomware infection. Those behind this attack ultimately published information stolen from some of Visser’s customers. Those organizations included defense contractors Lockheed Martin, General Dynamics, Boeing and SpaceX.
COVID-19 & Cyber Threats Report
As the ongoing COVID-19 (Coronavirus) pandemic spreads around the world, the unprecedented and evolving global situation has created numerous opportunities for threat actors to leverage the worldwide concern and anxiety in their nefarious campaigns. Cyberint Research is closely monitoring the cyber threats leveraging COVID-19 pandemic. As part of those activities, our team compiled a summary addressing the initial activities we detected.
Weekly Cyber Security News 27/03/2020
A selection of this week’s more interesting vulnerability disclosures and cyber security news. For a daily selection see our twitter feed at #ionCube24. With all the wild stuff going on right now, and I don’t know if it’s cabin fever causing regression, but I seem to home in on some almost retro items of news this week. The first, not so much that they were hit by a card skimmer, more that I didn’t realise they were still with us.