Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Ensuring your M&A delivers on its promise
Mergers and acquisitions (M&A) activity was muted at beginning of 2023, remaining consistent with the environment in the second half of 2022. But towards the tail end of 2023 activity started to pick up and looking ahead to 2024 deal-making is likely to accelerate. Volatility and uncertainty may have put a brake on activity in the short term, but smart investors will always see opportunities as valuations become more attractive.
Live API Attack Simulation
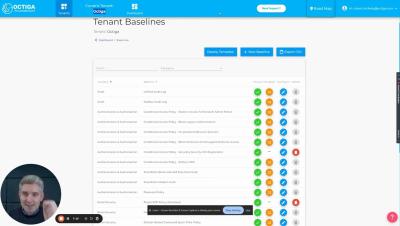
Octiga Demo Dec23
Applied Lessons from Product Security Teams in Vulnerability Management | Nucleus Security
BlueVoyant Acquires Conquest Cyber
Revolutionizing Business Horizons: An In-Depth Exploration of Cutting-Edge Business Software Development
Why Enterprises Choose Custom LMS Development Companies As Strategic Partners
Bringing Immutable Audit Trails to Dropbox
In the age of Gen AI, it is now apparent that we can no longer trust what we see and read. The fakers have the upper hand: while typical security approaches rely on scaling up teams, attacks scale at the press of a button. To safely move forward and realize the benefits Gen AI enables, we need a better trust model that adds integrity, transparency and trust to all data and a common provenance format that captures origin, authenticity and lineage information. We must verify data before we use it.