Reducing Scan Noise: False Positive Mitigation Strategies for MSSPs
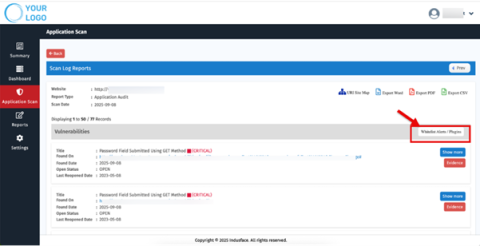
For Managed Security Service Providers (MSSPs), efficiency is everything. Every minute wasted chasing false positives is time that could have been spent on genuine threats, client communication, or platform improvement. Yet, excessive scan noise continues to plague many MSSPs, overloading SOC teams, distorting dashboards, and eroding client confidence.