Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Stability Unveiled: A Deep Dive into Stablecoins, Their Types, and Best Fit for Your Goals
How to Remove Candle Wax from Carpet
Secure your data with FIPS compliance in Endpoint Central
In today’s fast-paced digital landscape, security is not just a priority; it’s an imperative. We’re excited to announce a significant enhancement to Endpoint Central that will take your data security to a whole new level—Federal Information Processing Standards (FIPS) compliance. In this blog, we’ll explore what FIPS compliance is, why it matters, and how it can benefit your organization.
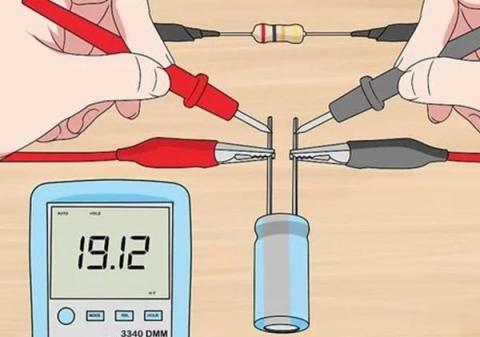
Safety First Shock-Free Capacitor Discharging Guide
CVE-2023-50916: Authentication Coercion Vulnerability in Kyocera Device Manager
FBI Releases Blackcat Ransomware Decryption Tool to Victims, Disrupting Attacks
For the first time ever, the U.S. Justice Department announced the existence of an FBI-developed decryption tool that has been used to save hundreds of victim organizations attacked by one of the most prolific ransomware variants in the world. In an announcement made last month, the Justice Department made the world aware of the existence of a decryption tool to be used by those organizations hit by Blackcat – also known as ALPHV or Noberus.
How Does PCI DSS 4.0 Affect Web Application Firewalls?
The payment industry is bracing for the transition to Payment Card Industry Data Security Standard (PCI DSS) 4.0, heralding significant changes in cybersecurity practices. As we approach the implementation of this revised standard, a critical focal point emerges: the role and new mandate of web application firewalls (WAFs) in ensuring compliance.
How to Reduce Your Attack Surface
An attack surface is the total number of channels, pathways, or areas that threat actors can utilize to gain unauthorized access to networks. The result is that they can obtain private information or carry out a cyber-attack. An attack surface comprises the organizational assets a threat actor can exploit to gain unauthorized access. Attack surfaces include systems that are directly involved in mission-critical operations, as well as those that provide peripheral services or access to important data.