Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Forward Networks Named 2023 Hot Company In Compliance By Cyber Defense Magazine's Top InfoSec Innovator Awards
Top tips: 3 common Zero Trust myths debunked
Top tips is a weekly column where we highlight what’s trending in the tech world and list ways to explore these trends. For the final week of Cybersecurity Awareness Month, we’re playing myth-busters and debunking three popular misconceptions about Zero Trust. Cyberthreats are becoming more and more brazen over time, and let’s face it—without a strong Zero Trust framework, your organization doesn’t have a dog in the fight.
SOX VS SOC - Mapping the Differences
Let’s explore the critical differences between SOC and SOX compliance. In the realm of information security and financial reporting, compliance enables organizations to build trust and transparency with stakeholders. To accomplish this, companies must adhere to specific regulations and standards. SOC and SOX represent two pivotal compliance frameworks that help maintain financial reporting integrity and data security.
Strengthening Security: The Power of Multiple Layers Against Advanced Threats
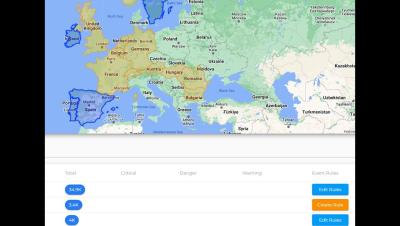
It's no secret that news of cyberattacks and data breaches that cause significant damage are becoming increasingly frequent in cybersecurity. Malicious actors are also constantly coming up with new threats, such as zero day attacks that are designed to avoid detection and bypass traditional security measures. It's crucial to take a comprehensive and global stance on this issue, rather than relying on a single security layer.
Level Up - SASE Accreditation and Practical Path to SASE
Email Routing subdomain support, new APIs and security protocols
It's been two years since we announced Email Routing, our solution to create custom email addresses for your domains and route incoming emails to your preferred mailbox. Since then, the team has worked hard to evolve the product and add more powerful features to meet our users' expectations. Examples include Route to Workers, which allows you to process your Emails programmatically using Workers scripts, Public APIs, Audit Logs, or DMARC Management.
DDoS threat report for 2023 Q3
Welcome to the third DDoS threat report of 2023. DDoS attacks, or distributed denial-of-service attacks, are a type of cyber attack that aims to disrupt websites (and other types of Internet properties) to make them unavailable for legitimate users by overwhelming them with more traffic than they can handle — similar to a driver stuck in a traffic jam on the way to the grocery store.
DC Board of Elections breach: Voter data is now online and up for sale
Earlier this month, the District of Columbia Board of Elections (DCBOE) warned that a threat actor may have gained access to the personal information of their registered voters. This would include personally identifiable information (PII) such as contact details, partial social security numbers, dates of birth, and driver’s license numbers. In an X post on Friday 20th October, the agency was keen to stress that it was only a possibility the voter roll had been accessed.
Phony Corsair job vacancy targets LinkedIn users with DarkGate malware
Job hunters should be on their guard. Researchers at security firm WithSecure have described how fake job opportunities are being posted on LinkedIn with the intent of spreading malware. A Vietnamese cybercrime gang is being blamed for a malware campaign that has seen bogus adverts posted on LinkedIn, pretending to be related to jobs at computer memory and gaming accessories firm Corsair.