Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Phishing Tests Start The Virtuous Cycle Of A Strong Security Culture
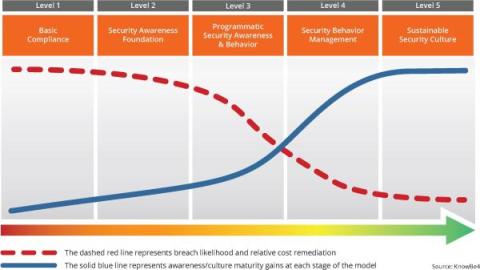
Phishing tests are the catalyst to achieve a sustainable security culture within your organization. They are actually the start of a virtuous cycle that helps you move up to the highest maturity level. The cycle initiates with Awareness. Phishing tests offer a real-time view into your employees' understanding of phishing threats. They expose your workforce to simulated phishing attempts, making the threat real to them. The immediate feedback from these tests highlights areas for improvement.
Summit Sabotage: Malicious Phishing Campaign Hits Female Political Leaders Using Social Engineering
A threat actor dubbed “Void Rabisu” used social engineering to target attendees of the Women Political Leaders (WPL) Summit that was held in Brussels from June 7 to 8, 2023, Trend Micro has found. “Since many current and future political leaders had attended this conference, it presented an interesting target for espionage campaigns and served as a possible avenue for threat actors to gain an initial foothold in political organizations,” Trend Micro says.
Cyber Insurers Notes Ransomware Claims Rose Significantly in the First Half of 2023
Cyber insurers are claiming that cybercriminals made ransomware attacks popular again in 2023 after a slight break in 2022. According to cyber insurer Coalition's 2023 Cyber Claims Report, claims frequency increased by 27% in the first half of this year compared to the second half of 2022. Additionally, cyber insurer Resilience Cyber Insurance Solutions mid-year report showed a similar trend with 16.2% of its total claims were related to ransomware attacks.
What is a CMDB?
There are countless tools and technologies available to help an organization stay on top of its IT assets, and a configuration management database (CMDB) is an extremely useful one. The database keeps track of relevant information regarding various hardware and software components and the relationships between them. It allows IT teams to have an organized view of configuration items (CIs) that can enable more streamlined processes when it comes to IT work.
Save the Embarrassment: The Value of Multi-Factor Authentication
These days, it’s not a matter of if your password will be breached but when. Major websites experience massive data breaches at an alarming rate. Have I Been Pwned currently has records from 705 sites comprising 12.6 billion accounts. This includes well-known names like Wattpad, Verifications.io, and Facebook.