Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Securing Our World
October is Cybersecurity Awareness Month, a dedicated month for the public and private sectors to work together to raise awareness about the importance of cybersecurity. And this year’s theme, “Secure Our World,” couldn’t be more timely. With the growing number of cyberattacks worldwide, it’s becoming increasingly apparent that critical infrastructure is at risk.
What is a Zero-Day (0-Day)?
In the world of cybersecurity, zero-day vulnerabilities, zero-day attacks, and zero-day exploits keep many CISOs up at night. These terms, often shrouded in mystery and intrigue, denote a significant risk to digital systems and the sensitive data they hold. Understanding the intricacies of zero-day vulnerabilities and the exploits that leverage them is crucial for individuals, organizations, and governments seeking to fortify their defenses against cyber threats.
Cyber Insurance - Does it Create More Problems than it Solves?
GhostLocker: The New Ransomware On The Block
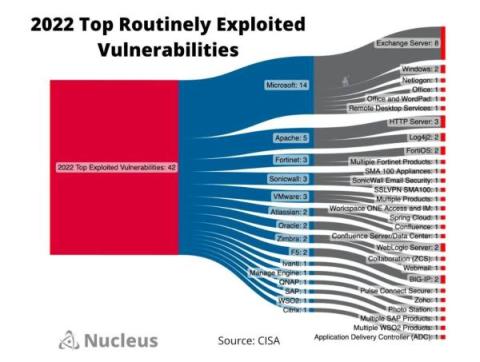
A Look at CISA's Top Routinely Exploited Vulnerabilities
BlueVoyant VISIBL
Learn more about BlueVoyant VISIBL: https://www.bluevoyant.com/services/visibl-vulnerability-identification-services
Powering the Future of Trust Management: Introducing Vanta AI
ManageEngine PAM360 now automates privileged access routines for over 800 enterprise apps-powered by Zoho Flow!
We are delighted to announce that ManageEngine PAM360 will now utilize Zoho Flow’s extensive product gallery to automate privileged access security workflows for more than 850 business applications and enterprise IT management tools.