Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Industry Trends and the Importance of Unified Identity Security
Slaying the many headed hydra of data privacy and protection
Office Hours: Fixing Vulns Live in the IDE Plugin Made Easy
What Is a SOC 2 Bridge Letter? With Examples!
Picture this: you’re a service organization that has aced your SOC 2 audit, and now your prospects are becoming customers at record speed as you prove your commitment to data security. But what happens in the interim period between one SOC report and the next? Enter the SOC 2 Bridge Letter, which fills the gap and keeps your compliance game on point. In this blog post, we’ll dive deep into the world of bridge letters, exploring their significance, components, and responsibilities.
5G's role in telemedicine: The future is now
Healthcare and technology have always gone hand in hand. Telemedicine, which lets you talk to doctors without visiting them in person, is a great example. A few years back, it might have sounded like science fiction. But today, it's a regular part of many people's lives. In fact, data shows that 80% of people have used telemedical services at least once in their lives.
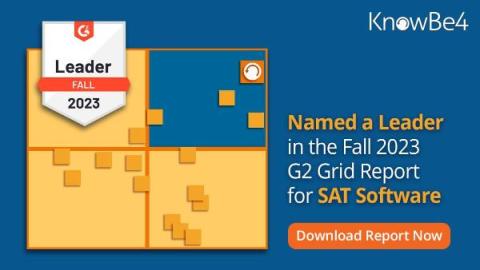
KnowBe4 Named a Leader in the Fall 2023 G2 Grid Report for Security Awareness Training
We are thrilled to announce that KnowBe4 has been named a leader in the latest G2 Grid Report that compares security awareness training (SAT) vendors based on user reviews, customer satisfaction, popularity and market presence. The latest G2 Grid Report compares Security Awareness Training (SAT) vendors based on user reviews, customer satisfaction, popularity and market presence.
Navigating the Cybersecurity Gender Gap: A Call for Change
As someone who has spent decades in the technology industry, I’ve seen the landscape transform dramatically. However, one issue remains persistent: the lack of gender and racial diversity in cybersecurity.
CrowdStrike Partners with Box to Add Automated Protections Against Security Breaches and Data Loss
The risk of cyberattacks continues to grow for small to medium-sized businesses (SMBs). Today, a staggering 70% of cyberattacks target SMBs, a scourge that cost organizations with fewer than 500 employees an average of $3.31 million USD in 2022, up 13.4% over the previous year. Adversaries tend to take the path of least resistance. This often means targeting small businesses, which face many of the same security threats as large organizations but lack the resources to defend against them.
Hackers Break into Flagstar Bank via Fiserv and MOVEit Vulnerabilities
Flagstar Bank is one of the largest national banks in the country. They operate over 430 branches and 120 banking teams from coast to coast. Flagstar is also the nation’s second-largest mortgage warehouse lender, servicing over 1.6 million accounts. Flagstar Bank’s conglomerate is based in New York, while their servicing is in Michigan. Flagstar oversees billions of dollars in loans, deposits, assets, and equity.