Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SBOMs: A Roadmap for a Secure Software Journey
Highlights From Impact Boston 2023
Open-source: The New Way of Envisioning Security
1.2 Million Patients Lose Data to Tampa General Hospital Breach
Tampa General Hospital is a mid-sized medical facility that caters to locals in the Tampa area. The hospital has 1,040 beds available and serves as a research and academic center, along with offering tertiary care to its patients. The facility is located in Tampa, Florida, and is an essential hospital for maintaining the care of patients throughout the area. The hospital was recently hacked, exposing more than 1.2 million patients that depend on the facility for medical services.
The Secret's Out: Researchers Reveal Backdoor in Emergency Radio Encryption
For over 25 years, a technology utilized for vital data and voice radio communications globally has remained under wraps, preventing in-depth testing for potential vulnerabilities. However, a small group of researchers in the Netherlands has now shed light on it, uncovering significant flaws, including a deliberate backdoor.
CloudCasa July Feature Updates
It’s been about three months since the last CloudCasa feature release in April, and we are now approaching the Dog Days of summer. These, as you may know, are named for the heliacal rising of Sirius, the Dog Star, in this sultry season, though the term more often conjures images of dogs lazing in the hot summer sun. We have been doing no summer lazing here at CloudCasa, though! Since our April release, we have focused much of our development effort on performance and reliability improvements.
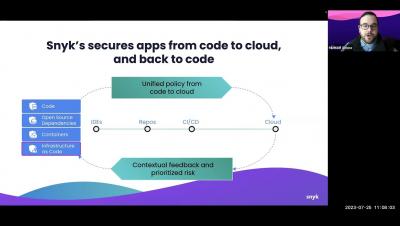
The New Era of AI-Powered Application Security. Part Three: How Can Application Security Cope With The Challenges Posed by AI?
This is the third part of a blog series on AI-powered application security. Following the first two parts that presented concerns associated with AI technology, this part covers suggested approaches to cope with AI concerns and challenges. In my previous blog posts, I presented major implications of AI use on application security, and examined why a new approach to application security may be required to cope with these challenges.