Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Netskope Threat Labs Stats for June 2023
Netskope Threat Labs publishes a monthly summary blog post of the top threats we are tracking on the Netskope platform. The purpose of this post is to provide strategic, actionable intelligence on active threats against enterprise users worldwide.
Weekly Cyber Security News 13/07/2023
A selection of this week’s more interesting vulnerability disclosures and cyber security news. Previously reported inside con job perpetrator has finally been sentenced. Such a dumb thing to do in both cases.
A Deep Dive into Penetration Testing of macOS Applications (Part 1)
As many of us know, there are a lot of guides and information on penetration testing applications on Windows and Linux. Unfortunately, a step-by-step guide doesn’t exist in the macOS domain to help us through the penetration testing process. This means we had to spend even more time searching the web and experimenting with different tools and techniques to find the most effective approach for our testing.
Theresa Payton on Identity Threats and the Chief 'Influence' Security Officer
You’re reading the CyberArk blog (and we thank you for that), so you’re likely familiar with the name Theresa Payton. The cybersecurity visionary, first female White House CIO, best-selling author and founder and CEO of Fortalice Solutions is a powerful industry voice, blending her frontline cybercrime fighting experience with cutting-edge insights to help organizations safely navigate the evolving threat landscape.
Combine Tines and OctoPerf to test your website's performance capability and automate custom load balancing tests
Tines has the superpower of protecting businesses in the security space through mission-critical automation workflows, but that does not mean our capabilities are restricted to that. In this blog, we’ll delve into how Tines can be implemented in other areas of the business to help your company streamline manual and time-consuming tasks.
How to Install Velero for Kubernetes Backups
Velero is an open-source backup and recovery tool designed specifically for Kubernetes clusters. It provides a straightforward way to protect your Kubernetes resources, including persistent volumes, namespaces, and custom resources, by taking backups and restoring them in case of data loss or disaster recovery scenarios. In this blog you will learn the different use cases for Velero and the two ways to install Velero, using the Velero CLI and using a Helm chart.
Insurance Services Company Imagine360 Gets Breached, Exposing 125k Individuals
Imagine360 is a Pennsylvania-based company that works with employers to develop custom health plans for their workers. The organization specializes in helping companies save money on insurance while giving better insurance to their employees. The company works with medium and large businesses and handles a large amount of data for its clients. Imagine360 LLC was recently a victim of two different file transfer data breaches, which means that health-related data and personal data have been exposed.
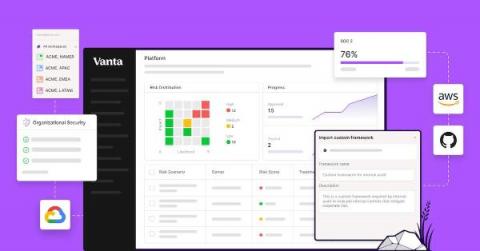
How Vanta combines automation & customization to supercharge your GRC program
As the industry’s first automated compliance platform, Vanta includes a wealth of pre-built content, which enables customers without existing compliance processes to quickly get up and running. But more mature organizations may already have a compliance program — from the processes they follow to the definitions of their compliance and security surface area — that is built to meet their unique compliance goals, auditor requirements, and tech stack.
Is the Dark Web Dangerous?
Yes, the dark web is dangerous because numerous criminal activities take place on the dark web. There are also cyberthreats that are common on the dark web such as malware, a type of malicious software, that can be installed onto your device by a cybercriminal and used to steal your information. Read on to learn more about why the dark web is dangerous and how you can avoid having your information published on it.