Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How NK's Cyber Criminals Stole 3 Billion in Crypto To Fund Their Nukes
The Wall Street Journal today revealed that North Korea's hacker army managed to steal a huge amount of cryptocurrency amounting to $3 billion to finance their nuclear program. US officials have confirmed this news. These hackers have a highly sophisticated method of operating. A specific example of their actions involved using a fake job offer to trick a startup into losing over $600 million. By posing as potential employers, they social engineered someone who was hopeful for a better job.
The Global Race for AI Dominance: Challenges, Data, and the Dangers of Falling Behind
Support Business Agility With Hybrid Cloud Services
Hybrid cloud takes the capabilities of the public and various private cloud options and merges them, allowing businesses to host different workloads within different environments depending on their performance, security, and resource needs. Companies leveraging a hybrid cloud strategy promote business competitiveness and agility, allowing them to respond to changes in resource demands quickly.
Infosec Growth in the Tech Industry: AI, Projects, and the Fourth Industrial Revolution
Penetration Testing 101: What You Need to Know About Pen Testing
Iran's uranium enrichment facilities were some of the most high-security buildings in the world. Not just with physical checkpoints and guards, but with air-gapped digital defenses. All of that security became moot in 2010 when Stuxnet devastated the facility.
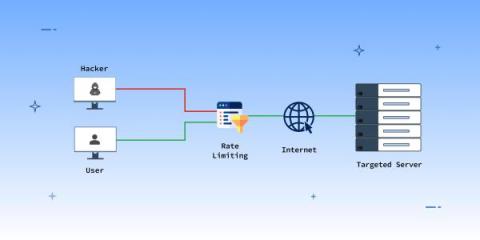
Preventing Denial of Service Attacks with Rate Limiting Techniques
A Denial of Service (DoS) attack will prevent your legitimate users from accessing your API. The attack could be physical, such as unplugging network cables, but a Distributed DoS is more prominent. It involves generating a volume of user requests from various machines to overwhelm your servers. DDoS attacks can result in a loss of $50,000 of revenue due to downtime and mitigation.
Verizon 2023 DBIR: Credential Leaks Continue To Be A Major Issue
Verizon's 2023 DBIR shows trends for incidents and breaches from the last year. Read our recap to see how credential leakage is helping malicious actors gain entry.
What's New in the NIST CSF 2.0 Draft?
The National Institute of Standards and Technology’s (NIST) Cybersecurity Framework (CSF) is undergoing a major update. The NIST CSF is one of the most widely used frameworks to help organizations understand and manage their cybersecurity risks. The NIST CSF was released as version 1.0 in 2014, updated to version 1.1 in 2018, and will be updated to version 2.0 early next year. NIST recently released a draft of CSF version 2.0.