Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Potential Surfacing of Cardpool's Gift Cards
Three Steps to Prevent a Cybersecurity Breach from MOVEit Exploit
SecurityScorecard conducted an extensive investigation into the Zellis breach. This research revealed alarming insights about the scale and persistence of the attack. The data exfiltration was carried out in several steps: Netflow data from Zellis IP ranges indicated large outbound transfers over HTTPS, which pointed towards the presence of a web shell. Additionally, SecurityScorecard researchers detected exfiltration over SSH to known malicious IP addresses.
Self-Managed Rules - AppTrana Feature Update Overview
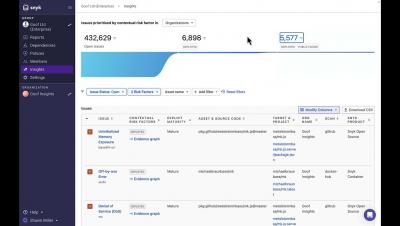
Using Insights (Snyk)
MOVEit and Lose it: Exploitation and Patching Hell
What is a Third-Party Data Breach?
A data breach is an IT security incident where data is compromised or stolen from a system without the knowledge or authorization of its owner. But what happens when a third party is involved? Stolen data may include sensitive, proprietary, or confidential information such as credit card numbers, trade secrets, customer, or patient data. Third party breaches cost millions of dollars every year to companies of all sizes.
As seen in Defence Connect: Managing information security risk to compete for AUKUS business
Outpost24 acquires external attack surface management provider Sweepatic to reduce risk exposure of internet facing assets
Outpost24, a leading cybersecurity risk management platform, today announced the acquisition of Sweepatic. Outpost24, a leading cybersecurity risk management platform, today announced the acquisition of Sweepatic. Based in Leuven (BE), Sweepatic is an innovative external attack surface management (EASM) platform. Gartner identified EASM as a top Security and Risk Management (SRM) trend for 2022.
Responding to the Critical MOVEit Transfer Vulnerability (CVE-2023-34362)
On May 31, 2023, Kroll received multiple reports that a zero-day vulnerability in MOVEit Transfer was being actively exploited to gain access to MOVEit servers. Kroll has observed threat actors using this vulnerability to upload a web shell, exfiltrate data and initiate intrusion lifecycles. This vulnerability may also enable a threat actor to move laterally to other areas of the network.