Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Kubernetes compliance under GDPR
Lie Machines - The global fight against misinformation
In this latest podcast in our ‘Beyond Data’ series, Tessa Jones (Calligo’s Chief Data Scientist) and Peter Matson (Data Science Practice Lead) talk with Oxford University’s Professor Philip Howard about the threats posed to democracy by technology, specifically in the shape of Lie Machines.
Centralized Log Management for SOX Compliance
NeoSystems Names Stuart Itkin Senior Vice President And CMO
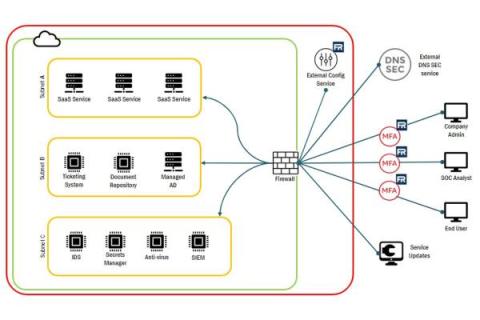
Understanding FedRAMP System Boundary
In the ever-changing world of technology, staying secure is a top priority for many organizations. Identifying and documenting system boundaries is essential for keeping data safe and secure, but what does this mean? In this article, we’ll explore FedRAMP System Boundary, how to identify them, and how to generate FedRAMP System Boundary diagrams.
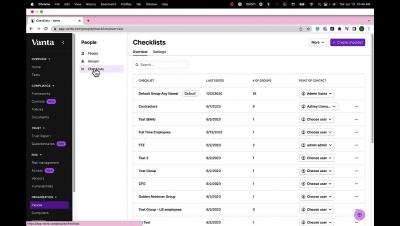
New in Vanta | May 2023
In May we announced Vanta Workspaces for customers with multiple business units, improved navigation bar labels & groupings, 15 new integrations, and more.
The Roadmap to Securing Your Digital Assets with Cybersecurity
“Technology trust is a good thing, but control is a better one.”
Risk Registers: The Ultimate Guide with Examples & Template
Effectively utilizing a risk register allows your organization to anticipate and overcome challenges with confidence. No GRC program is failproof, which is why it’s so critical to take a thorough look at potential risks and remediations. To make sure you’re starting on the right foot, we’ve provided a free, downloadable risk register template you can use once you have a better understanding of what it does.