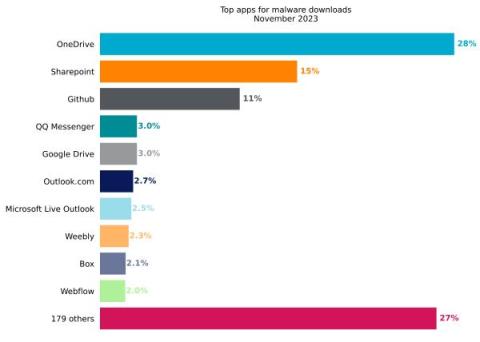
Netskope Threat Labs Stats for November 2023
Netskope Threat Labs publishes a monthly summary blog post of the top threats we are tracking on the Netskope platform. The purpose of this post is to provide strategic, actionable intelligence on active threats against enterprise users worldwide.