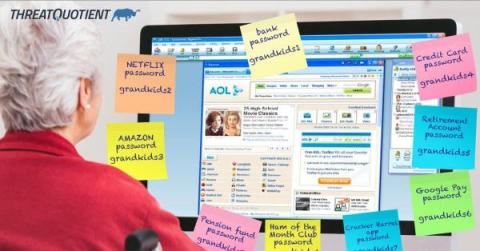
Fortify Your Security with Passwords and Password Managers
The internet has become an integral part of our daily lives, protecting our online accounts and sensitive information is more critical than ever. Passwords are the first line of defense against cyberattacks, and their strength is essential in safeguarding our identities. In this blog post, we’ll cover passwords and password managers, exploring the significance of strong passwords and the role that password managers play in enhancing our online security.