Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
No Ethical Boundaries: WormGPT
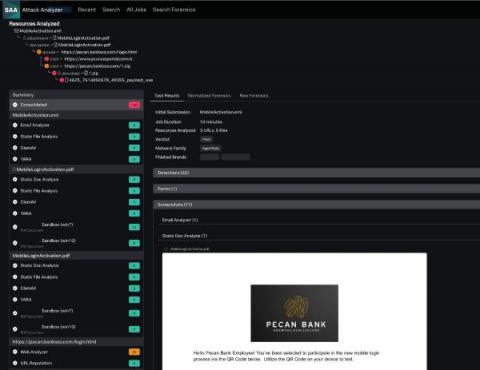
Eliminate Manual Threat Analysis of Credential Phishing and Malware Threats With Splunk Attack Analyzer
Greater Detection Accuracy and Faster Time-to-Value with Splunk IT Service Intelligence 4.17
What To Do If You Are A Victim of Cybercrime: The Anatomy Of High Profile Incident
Simplify Cyber Insurance (and Potentially Save Some Money) With Breach and Attack Simulation
Shifts in the threat landscape have caused cyber insurance providers to rethink how they offer and price their coverage. The result has been stricter underwriting requirements, more exclusions within coverage, and a dramatic increase in premiums. Tougher underwriting requirements have also put pressure on security and risk leaders to more thoroughly validate their security controls as enterprises are applying for, or renewing, their coverage.
A Message From the Dark Side: Your Defenses Will Fail, and Here's Why
I hear a lot of people compare securing their IT networks to how they would secure a house. But when most people turn the lock on their front door at night, they feel safe enough to go to bed and sleep peacefully.
Device Authority embraces transparency and international standards as the White House Names SBOMs as key pillar of Cybersecurity Implementation Plan
In a significant stride towards strengthening cybersecurity practices and protecting the nation’s digital future, the White House has issued a formal National Cybersecurity Implementation Plan, and named the 5 pillars that it believes are critical to successfully implementing its cybersecurity strategy.