Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
New Features Unlocked
Keeping your SLED Secure: Should you pay a ransom?
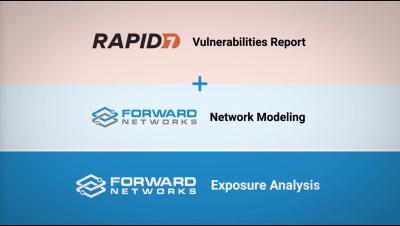
Forward Networks + Rapid7 InsightVM
Forward Networks + Tenable
AI is the Future of Cybersecurity. Here Are 5 Reasons Why.
While Gen AI tools are useful conduits for creativity, security teams know that they’re not without risk. At worst, employees will leak sensitive company data in prompts to chatbots like ChatGPT. At best, attack surfaces will expand, requiring more security resources in a time when businesses are already looking to consolidate. How are security teams planning to tackle the daunting workload? According to a recent Morgan Stanley report, top CIOs and CISOs are also turning to AI.
Advanced Persistent Threats Animation
Session management security: Best practices for protecting user sessions
Session management security is an essential component of web application development. It safeguards user sessions and prevents unauthorized access. Managing sessions secures the confidentiality, integrity, and availability of sensitive user data. It also protects user privacy at large — which is essential to maintaining user trust in an application. When we manage sessions securely, we establish processes to destroy session tokens when users log out or their session ends.
27 Cybersecurity Professionals and Business & Technology Leaders Reveal the Most Important Cyber Risk Trends Companies Need To Look Out for
Cyber risk trends are constantly evolving, driven by the pace of technological advancements that streamline business processes yet can introduce vulnerabilities in your company’s attack surface. With increased use of SaaS, cloud solutions, APIs, and third-party services, companies have many exposed and connected internet-facing assets that they’re unaware of, providing an open door for attackers to exploit.