Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Mass Exploitation of MOVEit Transfer Critical Vulnerability - Recommended Mitigations and How Forescout Can Help
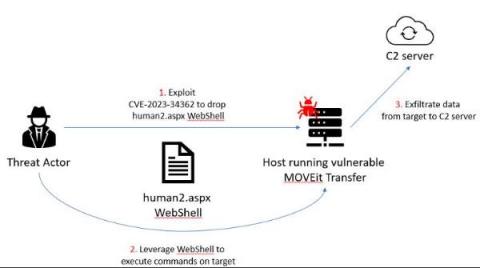
On May 31, Forescout Research – Vedere Labs uncovered a significant incident where threat actors exploited a critical zero-day vulnerability in the MOVEit Transfer software, which resulted in unauthorized access to and exfiltration of private data, as well as privilege escalation. MOVEit Transfer is a widely adopted managed file transfer (MFT) solution that enables organizations to securely exchange files with their business partners and customers.
Modify Mailbox Settings Via the Set-Mailbox Cmdlet
The Exchange Administration Center (EAC) is an easy-to-use interface for managing Exchange. However, it enable you to change only a handful of mailbox settings, and you can modify only one mailbox at a time. For more comprehensive management, you turn to Microsoft PowerShell (or, to be exact, Exchange Management Shell).
Shielding Against the Most Recent Fortinet Vulnerability
During a red team assessment for a client, Charles Fol and Dany Bach from LEXFO, discovered a heap overflow bug in Fortigate’s SSL VPN that can be exploited to achieve remote code execution on Fortigate instances. This vulnerability is reachable without authentication, and can be used to execute arbitrary code on vulnerable systems, which could lead to a complete compromise of the system.
Random but Memorable - Episode 11.0: Fancy Bear Grunge Nostalgia with Scott J. Shapiro
How do subdomain takeovers work?
Domain and IP intelligence with alphaMountain and LimaCharlie
Container Security Fundamentals - Linux namespaces part 1: The mount namespace
Introduction to Insights by Snyk
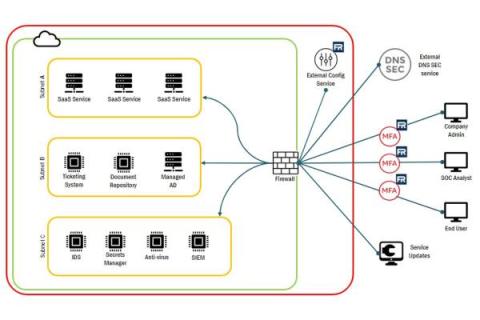
Understanding FedRAMP System Boundary
In the ever-changing world of technology, staying secure is a top priority for many organizations. Identifying and documenting system boundaries is essential for keeping data safe and secure, but what does this mean? In this article, we’ll explore FedRAMP System Boundary, how to identify them, and how to generate FedRAMP System Boundary diagrams.