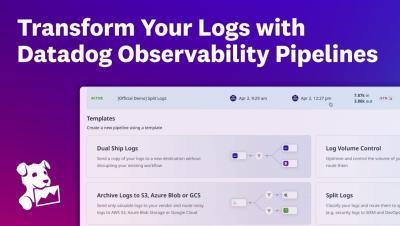
Enrich, Parse, and Control Logs with Observability Pipelines for Datadog Cloud SIEM
See how Datadog Observability Pipelines helps security and operations teams take control of their log data. In this demo, we’ll walk through: With Datadog, you can normalize, enrich, and prepare high-quality log data for Cloud SIEM, supporting faster investigations, more accurate detections, and reduced operational overhead—all without third-party software.