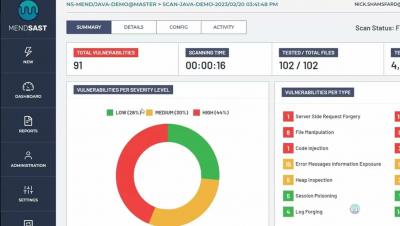
Gartner Hype Cycle for Application Security 2023 - Appknox Among Top Vendors in Mobile Application Security Testing
Gartner Hype Cycle for 2023 assesses the levels of maturity, adoption, and societal effects associated with emerging technologies in the field of Application Security. The 2023 report serves as a valuable resource for organizations seeking insights into the influence of security technologies on their applications. It also highlights the market leaders in the respective fields - Appknox being this year's leading vendor in mobile application security testing.