Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The latest News and Information on Application Security including monitoring, testing, and open source.
The Era of Automated SAST has Begun
For consecutive years, applications have remained the top attack vector for black hats, with supply chain attacks not far behind. At the same time, market research indicates that enterprise security managers and software developers continue to complain that their application security tools are cumbersome. When asked, many developers admit that they don’t run security tests as often as they should, and they push code to production even when they know it has security flaws.
Microsoft Power Pages: Low-code Misconfiguration Remains a Top Security Risk
Last week Dark Reading released an enterprise application security survey which raised serious concerns by IT and security teams Last week, Microsoft announced a new low-code application service called Power Pages, the fifth service joining the Power Platform. Whether you’re a low-code maker or professional developer, this low-code, scalable, and secure solution empowers you to build business-centric websites quickly and easily.
Automated Developer-First Security: Our Partnership with Snyk
Today’s developers move at increasingly rapid speed – making it more critical than ever to identify and resolve code vulnerabilities early in the software development lifecycle. By tackling security early – instead of waiting until testing and deployment – engineering teams can reduce unnecessary patching and maintenance cycles, reduce risks, and ensure timely delivery of new features.
SnykWeek Boston: Perspectives on developer security adoption
During SnykWeek Boston, Simon Maple (Field CTO, Snyk) led a panel discussion about developer adoption of application security. The panelists included: Want the TL;DR? Here are some of our favorite takeaways: Read on to dive deeper into these illuminating insights around organizing security teams, setting security goals, empowering developers, improving compliance, and much more.
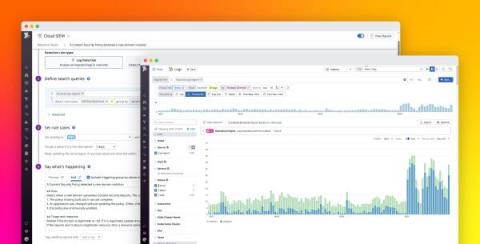
Monitor Content Security Policy violations with Datadog
Content Security Policy (CSP) is a W3C standard that helps defend web applications against cross-site scripting (XSS), clickjacking, and other code injection attacks. CSP is often deployed by using an HTTP header (or, less commonly, a element) to specify which types of resources are allowed to load on your site and where those resources can come from.
FedRAMP Certification: The 'New Normal' for Public Sector Agencies?
In the realm of cloud security, public sector agencies have a lot on their plates. From keeping up with the barrage of constantly emerging security guidelines (see below) to the ongoing demands of maintaining software security, the pressure on the government to lock down cybersecurity is immense.
Veracode Continuous Software Security Platform Overview
A Look Back at the Executive Order on Cybersecurity
It has officially been one year since the release of the Biden administration’s Executive Order on Cybersecurity, which outlines security requirements for software vendors selling software to the U.S. government. These requirements include security testing in the development process and a software bill of materials for the open-source libraries in use so that known vulnerabilities are disclosed and able to be tracked in the future, among other things.
What Is Software Supply Chain Security?
Most software today isn’t developed entirely from scratch. Instead, developers rely on a range of third-party resources to create their applications. By using pre-built libraries, developers don’t need to reinvent the wheel. They can use what already exists and spend time on proprietary code, helping to differentiate their software, finish projects quicker, reduce costs, and stay competitive. These third-party libraries make up part of the software supply chain.