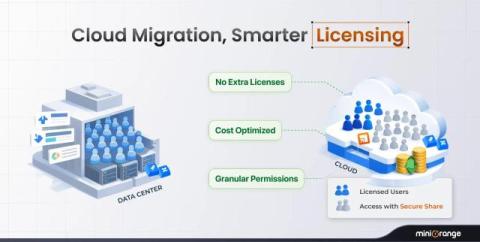
How Secure Share for Jira & Confluence Simplifies Atlassian Migration
Migrating from Atlassian Data Center (DC) to Cloud is a strategic move for many organizations. While migration brings scalability, flexibility, and cost benefits, it also introduces challenges, especially around secure external access, data sharing, and business continuity. This is where Secure Share for Jira and Confluence becomes a powerful ally.