Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Long Live The New King - Is Breached.co the New RaidForums Domain?
ARMO achieves SOC 2 certification: strengthening security and trust
5 Steps to Combating Emerging Threats with Network Security
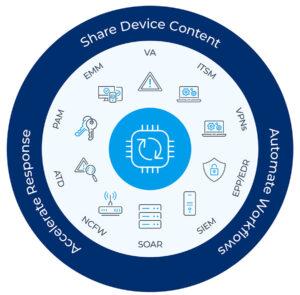
In today’s rapidly evolving threat landscape, cybercriminals have become more sophisticated than ever, making it crucial to stay abreast of the latest trends and tactics. The challenge is exacerbated by the expanding attack surface as more devices and device types connect to enterprise networks: IT, OT, IoT and IoMT devices, all with known vulnerabilities that can be exploited.
Unleashing the Power of Incident Reporting: Strengthening Security and Compliance
Whether it is reporting a phishing email or something that might be illegal that a coworker is doing, your employees should be a strong last line of defense for security and compliance. According to Gartner, almost 60 percent of all misconduct that is observed in the workplace never gets reported. For decades both compliance officers and security leaders have known that the earlier employees report incidents, the lower the risk. Yet low reporting rates continue to be a problem.
Russian Threat Actor Targets Ukraine Government And Military With Spear Phishing Emails
Russia’s APT28 (also known as “Fancy Bear” or “BlueDelta”) is using spear phishing to compromise Ukrainian government and military entities, according to researchers at Recorded Future. The phishing emails are designed to exploit vulnerabilities in the open-source webmail software Roundcube.
Enhancing Security and Asset Management with AI/ML in Cato Networks' SASE Product
We just introduced what we believe is a unique application of real-time, deep learning (DL) algorithms to network prevention. The announcement is hardly our foray into artificial intelligence (AI) and machine learning (ML). The technologies have long played a pivotal role in augmenting Cato’s SASE security and networking capabilities, enabling advanced threat prevention and efficient asset management. Let’s take a closer look.
CTI Roundup: New DoJ Cyber Unit Pursues State-Sponsored Threats
The DoJ launches a cyber unit to prosecute nation-state threat actors, cybercriminals use expired AWS S3 buckets to distribute malicious code, and a new exfiltration malware targets RDP workloads.