Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The latest News and Information on Application Security including monitoring, testing, and open source.
Threat modeling with Datadog Application Security Management
Threat modeling is a critical part of building high-performing, secure systems. It is responsible for “analyzing representations of a system to highlight concerns about security and privacy characteristics.”1 Creating an effective threat model involves two main steps: system modeling to map out all existing system components and the relationships between them, and threat elicitation to identify areas in the system that could be vulnerable to a security issue.
Enhance corporate application security with AWS Verified Access and Datadog
AWS Verified Access makes it easy and more secure for organizations to grant local or remote access to corporate applications without the use of a VPN. By using Verified Access, you can assign group policies to manage your organizations’ application access and administrative privileges at scale.
State of Application Security
Web application security is an important concern for organizations. Attacks have historically happened at the infrastructure and network level, but today, they increasingly target the business logic exposed by services that handle the most critical and sensitive data. The attack surface of applications is ever increasing, with more than 25,000 vulnerabilities identified in 2022 alone.
Datadog's Security Observability Day 2023
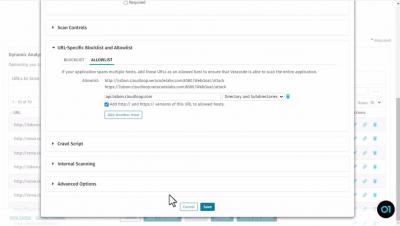
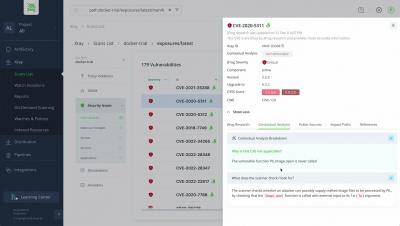
Create and Run an Unauthenticated Dynamic Analysis of a Web Application
Optimizing AppSec by Enhancing Integration with Jira
If there’s one thing we learned in our years of building AppSec technology, it’s that the best tools in the world are useless if they don’t get used. We know from speaking with our customers and industry research that developers won’t use AppSec tools that make their lives harder. Forcing them into cumbersome processes, or making them switch tools and learn a new user interface, will likely lead to AppSec neglect in favor of hitting development deadlines.
Warning: Poor Application Security Health Could Kill You
The Food and Drug Administration (FDA) recently implemented new guidance regarding medical device cybersecurity. It’s not a moment too soon, as new cases arise in which healthcare technology is compromised by vulnerabilities that escalate risks, which could threaten patients’ lives. In a recent survey, over 20% of healthcare organizations said that after a cyberattack, their patient mortality rates had risen, and another 57% reported that cyberattacks led to poorer outcomes for patients.
Why the Need for Application Security Intensifies as EU Tightens Cybersecurity Requirements
Two new sets of regulations introduced by the European Union (EU) indicate that the public sector is taking increased interest in improving cybersecurity and resilience. The EU is introducing the Digital Operational Resilience Act (DORA) for financial institutions and the Cyber Resilience Act (CRA) for software and hardware providers, both designed to enforce software security and secure delivery of services.