Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
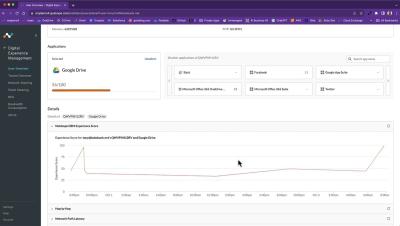
Demo - Netskope Digital Experience Management
Micro Lesson: Cloud SIEM MITRE ATT&CK Threat Coverage Explorer
Random but Memorable - Episode 11.5: Ethical Pizza Delivery Hobbies with Jamie Woodruff
The 443 Podcast - Episode 262 - Bing Chat Malvertising
How To Send Your Social Security Number Safely
The safest way to send your Social Security number (SSN) is by using a password manager. A password manager is a tool used to keep passwords and other sensitive data secure at all times. A little-known benefit to password managers is that in addition to generating and storing strong passwords, they also aid users in securely sending sensitive information such as Social Security numbers, MFA codes, home deeds, identification cards and more.
How does Vanta work? Top product questions about the Vanta Platform
Getting compliant can be a time-consuming and tedious process when done manually. That’s why thousands of businesses use Vanta to automate up to 90% of the work needed to comply with security and privacy frameworks. Why do companies choose Vanta? They’re looking to unlock business growth and expand into new markets or larger accounts, streamline their compliance processes, and strengthen their security posture to earn trust with stakeholders.
$3,000 of Gas Stolen from Hacked Pumps in Detroit
Detroit is Michigan’s largest city, hosting a population of more than 630,000 people. The area is called “Motor City” for its contributions to the automobile industry in the 1950s. More than 2.8 million cars belong to Detroit residents—and gas prices have reached a $3.72 gallon average. More cars are on the roads than ever before, but the cost of running them is taking its toll.
CVE-2023-42115: Critical RCE Vulnerability in Exim
What CIS Controls are Effective for Successful Cyber Defense?
Critical Security Controls are a set of cybersecurity principles and actions that list defense tactics and best practices to mitigate against popular cyber-attack methods. But what makes them so valuable is that the framework prioritizes a small number of actions that all work to significantly reduce cybersecurity risk across your network. Keep reading to learn more about CIS controls, as well as which controls are essential for successful cyber defense.