Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
DevSecOps Talks - Mitigating the Risks of 3rd Party Code
From Hesitation to Innovation: How Brands Can Successfully Navigate the Web3 Maze
Small Leaks, Billions Of Dollars - Cryptographic Exploits That Undermine Leading Crypto Wallets
Tutorial: Applying Parsers to Cloud SIEM Enterprise Data Sets
DevSecOps101: To Do or Not To Do
Coffee Talk with SURGe: The Interview Series featuring Derrick Lawson
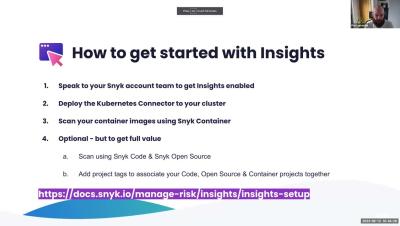
Office Hours: Insights - Focus on Top RIsks
Do You Know These Cybersecurity Basics?
There are many ways to safeguard your information online. Some cybersecurity basics you should already have down include using strong passwords, enabling Multi-Factor Authentication (MFA), regularly updating your software, limiting location sharing, not oversharing on social media, backing up your data and utilizing a VPN. Continue reading to learn more about what it looks like to implement these cybersecurity basics.
Best in Class
Why AWS indeed. This is not one of those start with why posts, but hopefully a peek into the reasons behind our partnership with AWS and what that means for you and how it could benefit you. The beginnings of something great Public cloud is well established, with about 50% of all workloads now running in a public cloud location. We have heard of ”the big three” cloud providers: AWS, Azure, and Google Cloud.