Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
WatchGuard Receives 2023 INTERNET TELEPHONY Friend of the Channel Award
Today, we are excited to share that WatchGuard was named a winner in the 2023 INTERNET TELEPHONY Friend of the Channel Awards! This prestigious award recognizes companies that run world-class channel programs that attract top MSPs and go the extra mile to support their partners.
Ekran System Introduces the SaaS Deployment Model
Easily Enable Encryption: Secure Cloud-native Development Series
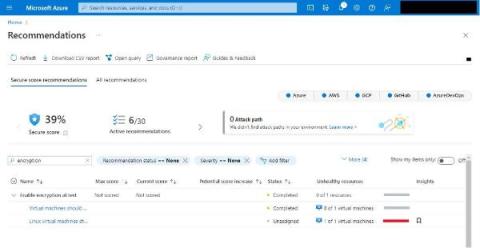
Build secure cloud-native applications by avoiding the top five security pitfalls we lay out in our Secure Cloud-native Development Series. This blog is the fourth part of the series, and it will teach you why and how to easily enable encryption and save yourself headaches down the road. Here's a new motto: encrypt everything! When securely moving to cloud-native technologies, building encryption in from the start will save us a lot of headaches later.
The Top 7 Cyberattacks on U.S. Government
In a world where ones and zeros are the new battleground, these threats, cyberattacks have become a significant threat to governments worldwide. The United States, with its vast array of government agencies and critical infrastructure, is no exception. Cybersecurity threats that impact the public sector range from state-sponsored attacks to financially motivated hacking groups. In this blog post, we’ll delve into the top 7 cyberattacks on the U.S.
How To Write A Post-Audit Cloud Security Report
A post-audit cloud security report is a document that provides an overview of the security status of the cloud environment, infrastructure, and applications of a business. It verifies that vulnerabilities and security flaws have been identified and assessed, and offers recommendations to address these security gaps.
Breaking Silos in Platform Security, Trust & Safety, and Risk - Mona Salvi (Sr. Director, HubSpot)
Software Supply Chain Security: The Basics and Four Critical Best Practices
Modern enterprise software is typically composed of some custom code and an increasing amount of third-party components, both closed and open source. These third-party components themselves very often get some of their functionality from other third-party components. The totality of all of the vendors and repositories from which these components (and their dependencies) come make up a large part of the software supply chain.
Policy-based routing with Egress Gateways
In this blog post I will be discussing how Egress Gateways can help in securing traffic by means of policy routing. If you are not familiar with Egress Gateways, take a look at our blog post, Using Calico egress gateway and access controls to secure traffic.