Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Falcon Cloud Security IaC Scanning: Demo Drill Down
CrowdStrike Counter Adversary Operations
Modern Strategies and Tools for Securing Internal Applications
Introducing Cloudflare's 2023 phishing threats report
After shutting down a ‘phishing-as-a-service’ operation that impacted thousands of victims in 43 countries, INTERPOL recently noted, “Cyberattacks such as phishing may be borderless and virtual in nature, but their impact on victims is real and devastating.” Business email compromise (BEC), a type of malware-less attack that tricks recipients into transferring funds — for example — has cost victims worldwide more than $50 billion, according to the FBI.
Centralized Log Management for TISAX Compliance
How our engineering team improves the on-call experience with Tines
This is the first of a series of posts about ways we use Tines at Tines to simplify our processes. I’m Izabela from the engineering team and will share how we improve the on-call experience with our own product. When it comes to on-call, there are differing views. For some, it comes as an easy and enjoyable task. For others, a stressful time on their calendars. At Tines, we have two types of on-call: daytime and out-of-hours.
How to Respond to Ivanti EPMM/MobileIron Vulnerabilities (CVE-2023-35078)
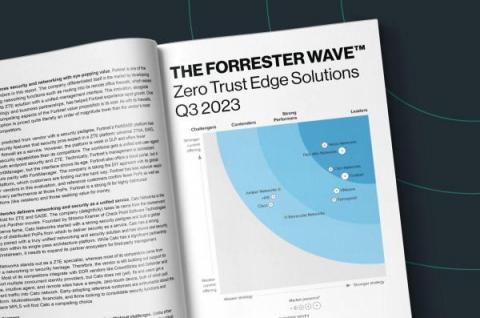
Cato named a Leader in Forrester's 2023 Wave for Zero Trust Edge
Today, Forrester released The Forrester Wave™: Zero Trust Edge Solutions, Q3 2023 Report. Zero Trust Edge (ZTE) is Forrester’s name for SASE. We were delighted to be described as the “poster child” of ZTE and SASE and be named a “Leader” in the report.