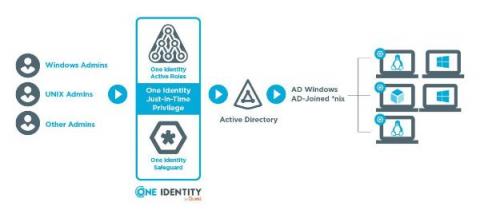
Just in Time Privilege Elevation in Active Directory
In my days of AD administration, there was always a need for a select set of sysadmins to be granted high levels of permissions. In AD, this is typically a separate user admin account that is a member of the Domain Admins Active Directory group. There are a few other groups that are highly privileged(i.e. Enterprise Admins and Schema Admins) but the permissions required by these groups are generally more specific and therefore less populated.