Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Vanta has joined the AWS ISV Accelerate Program
Today I’m excited to share the latest milestone in our growing partner ecosystem: Vanta has joined the Amazon Web Services (AWS) Independent Software Vendor (ISV) Accelerate Program. The AWS ISV Accelerate Program is a co-sell program for AWS Partners who provide software solutions that run on or integrate with AWS. Vanta’s acceptance into the program enables us to work in close collaboration with the AWS sales team to meet customer needs and provide better outcomes.
Secure by default: recommendations from the CISA's newest guide, and how Cloudflare follows these principles to keep you secure
When you buy a new house, you shouldn’t have to worry that everyone in the city can unlock your front door with a universal key before you change the lock. You also shouldn’t have to walk around the house with a screwdriver and tighten the window locks and back door so that intruders can’t pry them open.
How Financial Services Organizations Can Achieve Compliance and Reduce Cyber Risk
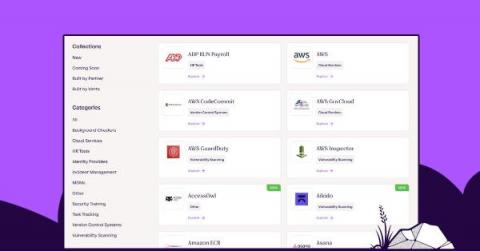
Vanta delivers over 50 new integrations in one quarter
We’re thrilled to announce that we’ve delivered more than 50 new system integrations over the past quarter, taking us to a total of 110 integrations. This is far ahead of any other automated compliance solution in the market, reflecting our innovation velocity and long-term commitment to ensuring customer value and success with Vanta.
Mobile Money Compliance: The Importance of AML Screening in 2023
Anti-money laundering (AML) compliance in the mobile money industry has become increasingly important in 2023. With the rise of mobile money transactions, regulatory bodies are ramping up efforts to combat money laundering and terrorist financing. In this infographic, we explore the technology involved in AML screening, the importance of AML compliance in the industry, and best practices for financial institutions.
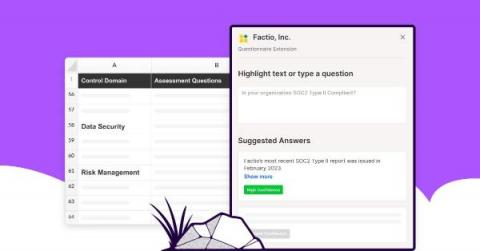
Introducing Questionnaire Automation
Following our recent acquisition of Trustpage, we are excited to announce Questionnaire Automation, a solution designed to help organizations in quickly responding to security questionnaires and effectively communicating security and compliance to customers and prospects. This solution utilizes the fastest and most accurate automation technology to provide security questionnaire responses.
SOC 1, 2, 3 Compliance: The 2023 Guide to Understanding & Achieving SOC Compliance
What is SOC 2 and how do you achieve SOC 2 compliance for containers and Kubernetes?
SOC 2 is a compliance standard for service organizations, developed by the American Institute of CPAs (AICPA), which specifies how organizations should manage customer data. SOC 2 is based on five overarching Trust Services Criteria (TSC): security, availability, processing integrity, confidentiality, and privacy. Specifically, the security criteria are broken down into nine sections called common criteria (CC).