Report: Attackers Can Trick AI Assistants Into Displaying Phishing Messages
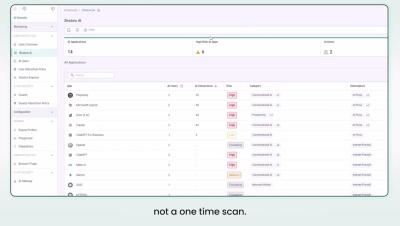
Researchers at Permiso warn that threat actors can plant phishing messages within Copilot AI summaries. Notably, the researchers found that attackers can trick Copilot into including internal information to craft a more targeted message.