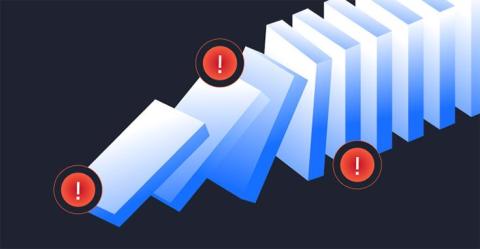
Shadow AI could be your organization's biggest threat.
What starts as innovation (an employee testing a new AI tool) can quickly become exposure. Unsanctioned apps create data leaks, compliance issues, and an expanded attack surface. With UpGuard User Risk, security teams gain visibility into shadow AI activity, so they can detect and neutralize risks before they escalate into breaches. activity before attackers can act. Ready to see what User Risk can do for you?