Risks and Challenges of Mismanaged Secrets
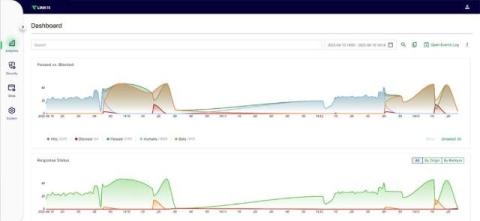
Mismanaged secrets put your business at risk of devastating data breaches and operational slowdowns. Watch this video to learn why you need a dedicated secrets management strategy and how Keeper can eliminate secrets sprawl.