Evolving Security Frameworks: From Compliance Checklists to Intelligence Engines
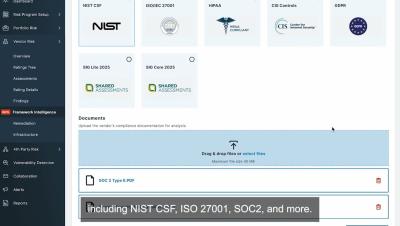
For years, security frameworks have served as essential tools for aligning cybersecurity practices, but they’ve also come with limitations. Designed primarily for compliance, many frameworks are rigid by nature, sometimes to the extent of being a checklist, making them ill-suited for today’s dynamic risk environments. But the threat landscape has evolved, and so too must our approach.